Why Small Businesses Are the Biggest Targets
There is a persistent myth that cybercriminals focus their energy on hospitals, banks, and Fortune 500 companies. The reality is the opposite. Attackers go where defenses are weakest, and small businesses overwhelmingly fit that description. You hold genuinely valuable assets: customer payment data, employee records, access credentials into client systems, and often years of proprietary business information. What you typically lack is a dedicated security team, enterprise-grade tooling, and the institutional knowledge to recognize when something has gone wrong.
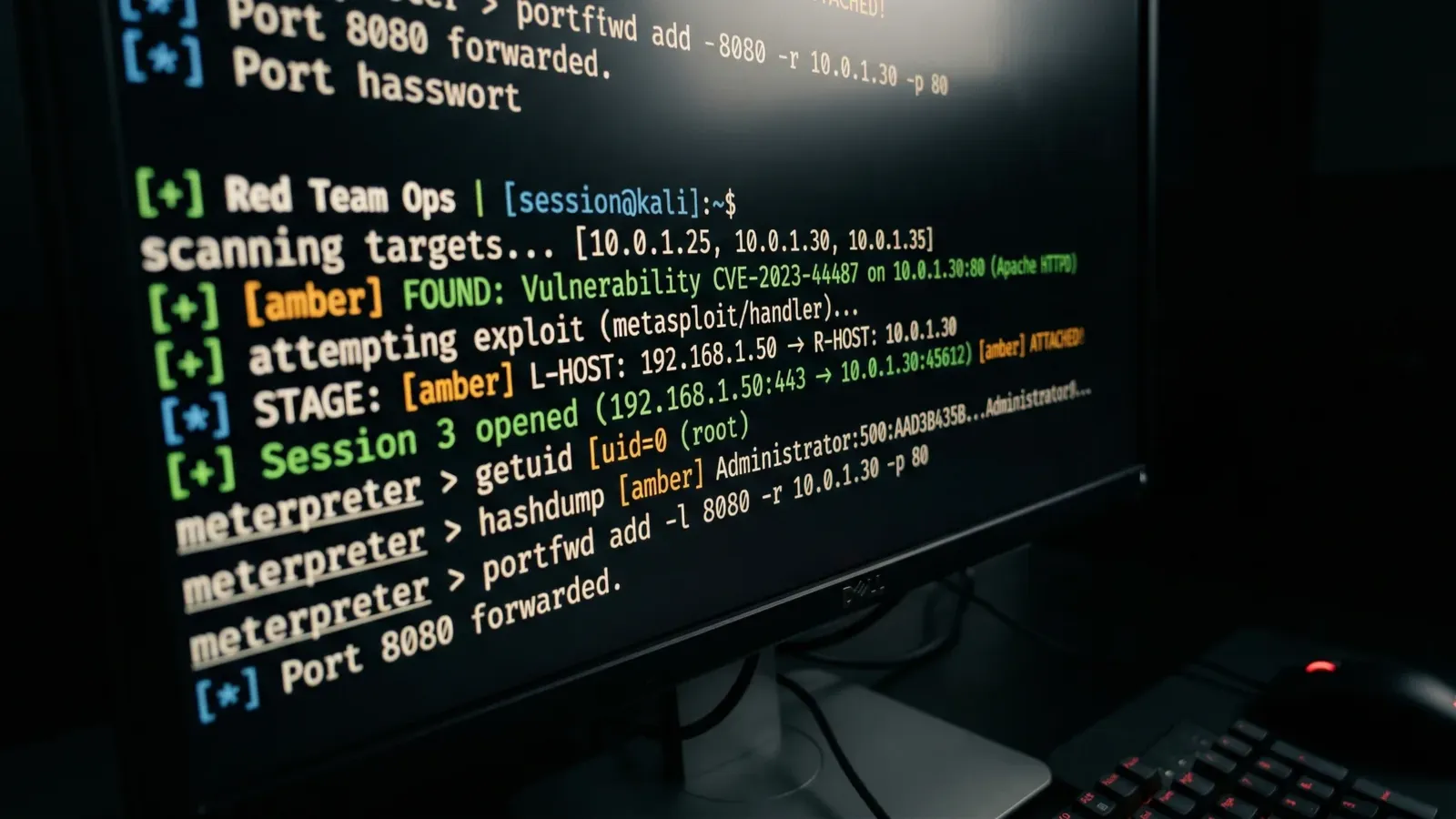
Ransomware operators have professionalized their operations to the point where targeting a hundred small businesses is more efficient than targeting one large enterprise. Automated scanning tools probe millions of internet-facing systems daily, looking for unpatched software, exposed remote desktop ports, and weak credentials. When a vulnerability is found, the intrusion is handed off to a human operator who moves through the network, disables backups, and deploys encryption. The entire process from initial access to ransom demand frequently takes less than 72 hours.
Phishing remains the dominant entry point. Business email compromise losses run into the billions annually across the economy. The messages have become convincingly realistic, impersonating vendors, executives, payroll systems, and banking portals. Without proper email filtering and trained employees who know what to look for, a single click is enough to hand an attacker full access to your environment.
The consequences are severe. Businesses that pay ransoms still spend weeks recovering operations. Businesses that refuse often lose data entirely. Regulatory penalties for data breaches involving personal or health information compound the financial damage. And cyber insurance carriers have tightened underwriting requirements significantly, leaving businesses with weak controls either uninsured or paying much higher premiums.
Our Cybersecurity Services
We do not sell a single product and call it cybersecurity. Effective protection requires multiple overlapping layers working together, because any one control can and will be bypassed by a determined attacker. Here is what we deploy and manage for our clients.
Endpoint Detection and Response
Traditional antivirus relies on recognizing known malware signatures. Modern attacks use custom code, living-off-the-land techniques, and fileless malware that never touches disk in a form signatures can detect. Endpoint Detection and Response takes a different approach: it monitors device behavior continuously and flags activity that looks malicious regardless of whether the specific threat has been seen before.
We deploy EDR agents on every managed workstation, laptop, and server. When a process begins encrypting files at unusual speed, attempts to dump credential stores, or establishes unexpected outbound connections, the EDR platform can automatically isolate that device from the network and alert our team. Containing a threat in its first minutes prevents it from spreading to every machine in your office. We review alerts, investigate suspicious activity, and handle remediation so your team never needs to understand what a memory injection attack looks like.
Email Security and Anti-Phishing
Your email gateway is the front door that attackers try first. We layer multiple controls on top of your existing email platform, whether that is Microsoft 365, Google Workspace, or another provider. Advanced filtering analyzes message content, sender reputation, link destinations, and attachment behavior before messages reach your inbox. Sandboxing detonates suspicious attachments in an isolated environment to detect malicious payloads that evade signature-based scanning.
We configure and enforce DKIM and DMARC records for your domain to prevent attackers from spoofing your outbound address to target your customers or partners. Quarantine management keeps flagged messages accessible for review without letting them reach end users. We tune filtering thresholds regularly to reduce false positives that cause staff to override security controls out of frustration.
- Multi-layer content and link analysis on every inbound message
- Attachment sandboxing to detonate suspicious files safely
- DKIM and DMARC enforcement to block domain spoofing
- Impersonation protection for executive and vendor names
- Quarantine with end-user review portal
- Regular tuning and policy updates
Security Awareness Training
Technical controls cannot stop an employee who has been convinced they are talking to their bank, their CEO, or a trusted IT vendor. Human error contributes to the majority of security incidents. Security awareness training addresses the layer that technology cannot fully protect: the decisions your people make every day.
We run ongoing phishing simulations using messages that mirror real attack campaigns currently active in the wild. When an employee clicks, they receive immediate feedback explaining the signals they missed and what they should do next time. We track click rates over time to measure whether training is working and to identify individuals who need additional coaching. Role-based training modules cover topics relevant to each employee's function: finance staff learn to recognize payment redirect fraud, HR staff learn to spot credential harvesting, and executives learn to identify CEO impersonation attempts. Training that is relevant to an employee's actual job responsibilities sticks far better than generic security lectures.
Vulnerability Assessments
You cannot defend what you do not know exists. Many businesses accumulate systems, software, and configurations over years without any systematic review of what exposure that creates. A vulnerability assessment gives you a clear picture of your attack surface and prioritizes remediation by actual risk rather than theoretical severity scores.
Our assessments include external network scanning to identify what is visible from the internet, internal scanning to find unpatched systems and misconfigurations on your local network, and credential testing to identify accounts with weak or reused passwords. For clients requiring more rigorous validation, we conduct penetration testing that simulates real attacker techniques to see how far an intruder could get given initial access.
Every assessment concludes with a written report that identifies findings, explains business impact in plain language, and provides a prioritized remediation plan with specific technical steps. We do not hand you a raw scanner output and leave you to interpret it. We walk through findings with your team and track remediation completion to ensure gaps are actually closed.
Dark Web Monitoring
When companies suffer data breaches, stolen credentials are typically sold or shared on criminal forums, paste sites, and dark web marketplaces within days. Employees who reuse passwords across personal and work accounts become an attack vector the moment their personal credentials appear in a breach. Attackers purchase credential lists in bulk and run automated login attempts against business applications, VPN portals, and email systems.
Our dark web monitoring service continuously scans these sources for your business email domains, employee addresses, and key credentials. When your data appears, we alert you immediately with enough context to take action: which account was exposed, what breach it came from, and what steps to take next. Prompt detection and forced password resets can close this exposure before it becomes an incident.
Compliance Support
Regulated industries face security requirements that go beyond general best practices. Non-compliance can mean losing contracts, facing regulatory penalties, or being unable to obtain cyber insurance coverage. We help businesses navigate the security requirements of the frameworks most relevant to Pacific Northwest industries.
For healthcare organizations, we provide HIPAA security rule compliance support including risk analysis, policy development, workforce training documentation, and technical safeguard implementation. For government contractors handling controlled unclassified information, we work toward CMMC Level 1 and Level 2 requirements, building the documentation and controls needed to pass assessments. For businesses seeking or renewing cyber insurance, we identify the specific controls underwriters require and help implement them before the audit.
- HIPAA Security Rule gap assessment and remediation planning
- CMMC Level 1 and Level 2 readiness support
- Cyber insurance pre-audit preparation
- Security policy and procedure documentation
- Workforce training documentation for compliance records
- Technical control implementation and evidence collection
Industries with Elevated Security Requirements
Every business needs cybersecurity, but some industries carry additional regulatory obligations, handle more sensitive data, or face more targeted threat actors. We have deep experience with the specific security requirements these sectors face.
Healthcare
Patient records are among the most valuable data types on criminal markets. HIPAA requires documented risk analysis, access controls, audit logging, and workforce training. We help clinics, dental practices, and healthcare-adjacent businesses build compliant environments without disrupting clinical workflows.
Legal
Attorney-client privilege and ethical obligations make data security a professional responsibility, not just a business concern. Law firms hold sensitive client information, opposing counsel strategies, and transaction details that make them attractive targets. We secure document management systems, email, and remote access for firms of all sizes.
Financial Services
Accounting firms, financial advisors, and insurance agencies handle client financial data subject to state and federal regulatory frameworks. Transaction fraud, wire redirect schemes, and credential theft target financial sector businesses disproportionately. We deploy controls that address both regulatory requirements and the specific attack patterns financial firms face.
Construction
Project data, bid information, subcontractor relationships, and contract terms represent real competitive value worth protecting. Construction firms working on public projects increasingly face requirements to demonstrate security controls. Business email compromise targeting payment redirect is common in the industry.
Government Contractors
Businesses handling controlled unclassified information must meet CMMC requirements to maintain federal contracts. The compliance burden is substantial, and the consequences of failing an assessment or suffering a data breach involving CUI are severe. We help defense contractors and federal subcontractors build and document the required controls.
Layered Security, Not Silver Bullets
Vendors selling single-product security solutions have a financial incentive to convince you that their tool is sufficient. It never is. No firewall stops every threat. No email filter catches every phishing message. No EDR platform detects every novel attack technique. Effective cybersecurity is not about finding the perfect product; it is about building enough overlapping layers that an attacker must defeat multiple independent controls to reach their objective.
This principle, called defense in depth, has been the foundation of military and physical security for centuries. Applied to IT, it means your email filter catches threats that perimeter firewalls cannot inspect. Your EDR catches threats that the email filter missed. Your security awareness training means employees do not open the attachment that slipped through the filter. Your dark web monitoring catches the credential that would have given an attacker a foothold even if they had not used email at all. And your vulnerability assessments identify the unpatched software that would have given them persistence after gaining access.
We design security stacks for the actual threat landscape small and mid-size businesses face: opportunistic attackers running automated tools, ransomware groups targeting organizations below the enterprise threshold, and business email compromise operators who do patient reconnaissance before making their move. We do not oversell controls that protect against nation-state threats you are unlikely to face. We focus on the protections that prevent the incidents that actually happen to businesses like yours.